- Kerberos: Dieses Validierungsprotokoll bietet stabile Authentifizierung für Client-Server-basierte Anwendungen durch Verschlüsselung mit geheimen Schlüsseln. Kerberos geht davon aus, dass alle Endpunkte innerhalb eines Netzwerks unsicher sind. Es erzwingt daher jederzeit eine starke Verschlüsselung
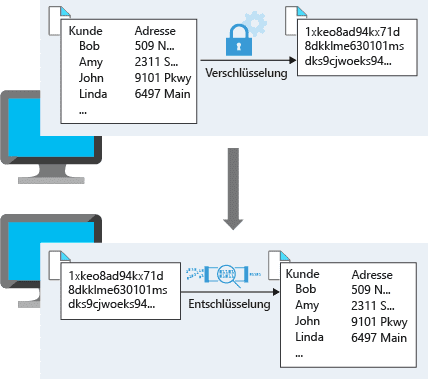
Verschlüsselung ist der Vorgang, bei dem Daten für unberechtigte Betrachter nicht lesbar und nicht verwendbar gemacht werden. Um verschlüsselte Daten verwenden oder lesen zu können, müssen sie entschlüsselt werden. Hierfür ist ein geheimer Schlüssel erforderlich. Es gibt zwei Arten von Verschlüsselungen auf oberster Ebene: symmetrisch und asymmetrisch. Bei der symmetrischen Verschlüsselung wird zum Verschlüsseln und Entschlüsseln der Daten jeweils der gleiche Schlüssel verwendet. Erwägen Sie die Verwendung... mehr erfahren für die gesamte Kommunikation und alle Daten.
Dieser Beitrag ist auch verfügbar auf:
English (Englisch)